What's the Difference Between SIM, eSIM, and iSIM?
This article appeared in Electronic Design and has been published here with permission.
What you’ll learn:
The cost prohibition presented by physical SIMs in today’s growing IoT ecosystem.
The advent of eSIM to overcome scalability issues.
How eSIM and iSIM can open up new IoT opportunities.
The typical smart home in 2020 had, on average, 50 connected IoT devices—and that’s contributing to the 35 billion devices we as consumers are expected to own by the end of 2021. The scale of industrial deployments that allow enterprises to deliver the services we rely upon, such as our electricity, water, gas, or the reliability of supply infrastructure of food, medicines, etc., is significantly larger.
The adoption of 5G is going to accelerate this deployment of connected devices. But as with most disruptive new technology waves, 5G brings its own challenges, causing designers to consider how they support new radio bands and adding complexity to IoT device design.
Increasingly, the devices in question are low power, long-lived in field, low cost, and afford low levels of physical access, plus they’re deployed across further distances and remote locations. Cellular IoT’s ubiquitous connectivity is a key draw for designers in fast-growing markets, such as infrastructure, for more intelligent transport, smart consumer and smart city devices, and connected health.
Cellular IoT has long been the choice of secure, large-scale, and resilient deployments due to the robust subscriber identity module (SIM) that authenticates a device. As our devices shrink, and as remote devices must endure a much wider range of environmental conditions, securing the device’s identity requires new and broader solutions.
It’s not just the physical design that’s a consideration when leveraging SIMs and cellular IoT. Scale is both the IoT’s most significant opportunity and hurdle, and organizations need to consider how they will manage and secure the device throughout an extended lifecycle.
Think about some of the use cases that 5G will enable in smart cities and logistics. The deployment, management, and swapping of physical SIMs to update user profiles or switch network providers in these remote locations presents a considerable cost to OEMs and end users alike.
Introducing the eSIM
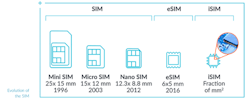
Embedded SIM (eSIM) technology is still a hardware-based SIM, but this elegant, robust, and scalable technology is soldered permanently into the device and was designed to address some of the challenges impeding true scalability in cellular IoT (see figure). eSIM allows devices to be deployed anywhere with existing cellular coverage. Operator profiles or network providers can be updated over the air, based on standards that offer a frictionless experience for device manufacturers and service operators.
iSIM Builds on eSIM
But there’s more: An integrated SIM (iSIM) takes all of the benefits of eSIM and embeds them into the device’s permanent hardware array by combining the SIM with the system-on-chip (SoC) architecture and cellular modem. Fusing the secure locations into the chipset itself offers a low footprint. It also introduces extra layers of security through a hardware-based secure enclave (a dedicated processor for security operations) that maintains the integrity of all cryptographic and key managed operations.
Security and Scale Go Hand-in-Hand
As the number of devices ramps up, the IoT attack vector will grow exponentially—security can’t be an afterthought. IoT continues to move closer to core processes, and businesses should ensure that both devices (i.e., the endpoint itself) and data exchange (in technical terms, the chip-to-cloud security) have strong identity and trust foundations.
To achieve scale, enterprises need simpler ways of manufacturing while being able to keep the robust security benefits derived from SIM capabilities. This has typically proven to be a challenge as new market needs for IoT are emerging.
The fastest growth of eSIM and iSIM deployments is coming from markets that haven’t traditionally operated at the same cost points as cellular or smartphone industry. Markets such as fleet management of e-bikes or e-scooters, or connected health wearables, didn’t exist in their current capabilities a few years ago.
Within these, enterprises need simplification of both the bill of materials and that of the supply chain. iSIM fundamentally changes the way device makers can access cellular capabilities for devices that couldn’t be served before. iSIM offers the highest protection for subscription credentials and isolates processing in a secure enclave. An additional authentication layer serves as a root of trust for secure communications while reducing the bill of materials.
The GSMA standard IoT-SAFE (IoT SIM Applet For Secure End-2-End Communication) for iSIM supports the entire secure chip-to-cloud IoT infrastructure. It allows iSIMs to authenticate both connectivity and application credentials for any data being exchanged with any cloud over any cellular network by any device.
New Opportunities
eSIM and iSIM are solutions to existing problems, but they also open up new opportunities for the broader IoT ecosystem:
“In the IoT space, cost is everything and this is where iSIM stands out. Their significant cost difference enables cellular applications that weren’t previously viable. It’s a whole new IoT world that we’re just starting to explore. And iSIM makes this new world possible.”—Alex Sinclair, GSMA Chief Technology Officer
Device and module makers benefit from more streamlined processes, such as reducing SKUs that contain multiple SIMs for individual regions, freeing them to focus on value-add services in a number of use cases. For example, we’re seeing logistics companies utilize cellular M2M devices featuring multiple device sensors powered by eSIM technology to provide live global tracking. Smart energy providers are turning to low-power wide-area networks (LPWANs) to deploy their eSIM-enabled smart energy devices globally.
In our cities, automotive OEMs are tapping into 5G to power their “cellular vehicle-to-everything” (C-V2X) service, serving as a means for cars to communicate with everything around them. Meanwhile, IoT service providers can expand beyond the constraints of Wi-Fi without the need for costly infrastructure by tapping into LTE-M and NB-IoT technology, exposing them to greater market opportunity
The use cases are as broad as they are attractive. eSIM and iSIM are paving the way for centralization of agricultural operations as smaller, less expensive tracking devices can be deployed in remote, rugged terrain. And global logistics providers can track more assets in real-time with low-power M2M modules that go for months between charges. The opportunities presented by cellular IoT, underpinned by 5G, are abundant. iSIM technology is reducing complexity and cost as well as providing the secure foundation that will allow the IoT to scale in the 5G wave.
About the Author
Vincent Korstanje
CEO, Kigen
Vincent Korstanje is CEO of Kigen, an Arm company. Vincent’s mission is to make eSIM and iSIM the foundation of all connected devices, which led him to form the Kigen group in Arm in 2016. Kigen became a separate company in October 2020 to drive this vision to secure trillions of connected devices. Vincent worked for Arm for 22 years, in which he helped build the UK’s leading technology company. Before Arm, Vincent worked at TNO in compiler and security technology.