Cybersecurity is Imperative for Connected Cars
What you’ll learn:
- How can contemporary vehicles be hacked?
- When should security be designed into an automotive system?
- Overview of various successful techniques and processes to protect cars against cyberattack.
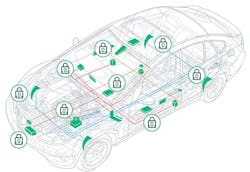
Today’s vehicles are essentially software on wheels, comprising complex and often interrelated collections of automotive systems such as braking, power locks, steering, entertainment, window controls, and so on. In addition to those cool capabilities, next-generation cars are adding a plethora of features, from autonomous operation to advanced driver-assistance systems (ADAS), which only increase the overall complexity. Overall, the skyrocketing amount of electronic control units (ECUs) in vehicles and addition of new communication interfaces presents a rich field of opportunities for hackers (Fig. 1).
Safety and security experts are paying greater attention to the growing number of connected cars on the road. More than 18 million new automated vehicles are expected to hit the roads by 2030 (Frost & Sullivan). Unless automotive manufacturers and suppliers strive to build security into cars from the beginning, this influx of connected cars will carry increased risks on both the personal and business disruption levels.
Any new Internet of Things (IoT) device opens another vulnerability point. When those “devices” are vehicles transporting people at high speeds on roadways, these vulnerabilities become safety risks.
This isn’t just a theoretical problem for future cars. In fact, two-thirds of new cars registered in the UK today already are connected, according to the Society of Motor Manufacturers and Traders (SMMT). Such connectivity is great for advanced telemetry services, over-the-air updates, and delivering content for in-vehicle infotainment (IVI) systems. It also means the car is connected to the internet, so communication, as well as risk, is a two-way street.
While the vehicle can send helpful data about the driver and the car to the manufacturer, the mechanisms that control its movement, such as steering, braking, and acceleration, can all be hacked by hostile actors if the car’s ECUs aren’t authenticated and secure.
A major threat lies in a hostile actor infiltrating the communication or control networks that connect the cars, enabling an attack against an entire fleet. Such an attack potentially can require few resources and could harm many passengers, vehicles, and pedestrians.
Taking Secure Measures
So how do we ensure every automotive communication end point is authenticated and using encrypted communications?
Security must start early in the design and specification process (Fig. 2). Connected-vehicle technology progresses at lightning speed, and security must not be an afterthought.
We currently lack worldwide standards to ensure that every device (including vehicle components) is known, authentic, and secure. Connecting the car to the internet happens via chips and code. However, despite the critical nature of these components, all too often manufacturers have no visibility into their own supply chain. Thus, they remain unaware of whether the open-source code they’re using contains malicious elements or the selected chip is appropriately verified to guarantee its safety.
This lack of knowledge means security weaknesses could be present in systems even before they are complete. Ensuring that security standards are imposed on the entire supply chain is of paramount importance.
One aspect of security is ensuring the authenticity of all components throughout the entire supply chain. Digital certificates can be utilized for this purpose. Issued by a trusted Certificate Authority, certificates can be inserted into devices and components to confirm that the component is authentic. In a sense, a digital certificate is like a valid license plate for an IoT device. And like license plates, no car should be allowed on the road without one.
In addition to certificates, an increasing number of auto manufacturers are layering on security technologies such as embedded firewalls, secure boot, and secure firmware updates.
Embedded firewalls enable automotive ECU suppliers to enforce filtering rules and detect anomalies in network communications to prevent cyberattacks. Secure boot ensures that the firmware and software running on the car is authentic and hasn’t been modified by hackers, and secure firmware updates allow car manufacturers to patch the firmware for security updates as well as add new features. Together these security technologies maximize driver safety and help prevent the loss of intellectual property, disruption of services, and proliferation of attacks on other systems.
The legislatures of the UK, Australia, and the State of California have begun to implement or draft IoT security regulations. But until security technologies are the norm and not the exception, ad hoc regulations still leave the door open for rogue devices to enter the network, infect it, and force other connected devices to misbehave, including vehicles traveling at high speeds on busy roads.
The trend in connected vehicles shows no signs of winding down, so correcting blatant security failings is an imperative. Manufacturers putting vehicles on the road should be held accountable for the safety of their product, and resilience to cyberattacks should be one more factor in their quality controls.
Summary
Automobiles are an essential part of our lives. Imagine what could happen if a cyberterrorist were able to take control of a moving vehicle. Imagine the financial damage that could ensue if a bad actor were to hack an entire fleet of vehicles and prevent them from operating unless a suitable ransom was paid?
When adding security to a complicated device like a car, it’s imperative that system developers ensure the vehicle is resilient to common attacks and includes multiple layers of security. Anything less is simply not good enough—especially for the next generation of smart, autonomous vehicles.
Alan Grau is VP of IoT/Embedded Solutions at Sectigo.
About the Author
Alan Grau
VP of IoT/Embedded Solutions, Sectigo
Alan Grau has 30 years of experience in telecommunications and the embedded software marketplace. He is VP of IoT/Embedded Solutions at Sectigo (https://sectigo.com/quantum-labs), a provider of purpose-built, automated public-key infrastructure (PKI) solutions. Grau joined Sectigo in May 2019 when it acquired Icon Labs, a provider of security software for IoT and embedded devices, where he was CTO and co-founder. He is a frequent industry speaker and blogger and holds multiple patents related to telecommunication and security.
Prior to founding Icon Labs, Grau worked for AT&T Bell Labs and Motorola. He holds an MS in computer science from Northwestern University.