Download this article in PDF format.
Firearms are constantly subjected to regulations and legislation in attempts to control access and limit operation only to authorized users. Many efforts have been made to track the critical components of a firearm throughout its operating lifetime, with one of the most critical firearm components referred to as the receiver. The receiver contains the trigger and the bolt. The receiver is often the only portion of a firearm that’s federally regulated and required to be serialized.
Recent development of miniature, mechanically robust radio-frequency-identification (RFID) tags provides the means of tracking firearms and their receivers in difficult environments. To demonstrate this new capability, small RFID tags will be used to track the lower receivers in AR-15 family firearms for smart gun applications.
The AR-15 lower receiver (LR) has been chosen initially for a number of reasons. It’s the only component in the rifle that requires federal regulation and is serialized, making it the prime candidate for tracking. The LR being the main mechanism of the rifle also requires a significant level of routine maintenance, which makes it ideal for automated RFID tracking applications.
Additionally, this family of semiautomatic rifles is one of the broadest and most popular in the world (automatic versions include the M4 and M16). Since each RFID tag incorporates an integrated circuit (IC) with an unalterable unique identification number (UID), it provides tracking by association with the federally regulated serial number of the component. The unalterable functionality is a requirement of currently proposed new legislation (NJ Bill A1016, which also mentions the use of RFID).
By means of RFID, the receiver is well-suited to act as the “custodian” of a firearm’s history by recording within an RFIC tag’s IC any pertinent information of any components that are part of the assembly. Information can be stored within any RFID IC that also contains programmable memory in addition to its UID. The storage of information occurs within the RFID tag, whose IC also has a programmable memory in addition to its UID.
Furthermore, the UID has the functionality to track/identify the original serial number of the receiver, making it possible to identify firearms when the serial numbers are removed. The RFID IC’s programmable functionality can also be locked, making it unalterable if required.
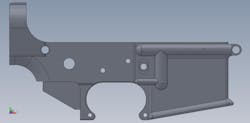
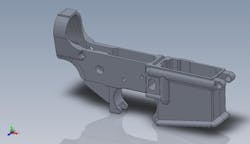
Figures 1 and 2 provide a number of different views of an AR-15 LR. They are typically forged from a lightweight aluminum alloy (7075-T6), but can also be made from steel or a composite material. This current study has focused on metal receivers, since they are more common and more challenging in terms of performing tracking by means of RFID technology.
1. This is one view of the lower receiver (LR) for an AR-15 firearm.
2. Here’s a second view of the LR for an AR-15 firearm.
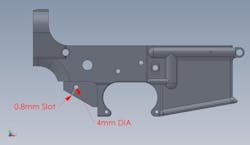
An initial investigation identified the area covered by the pistol grip (which is typically nonmetal material) as the optimal location for the RFID tag. This area offers sufficient structure to house a small RFID tag flush-mounted on the surface. As such, the pistol grip can be installed without issue or any need to change the firearm assembly procedure. The pistol grip also provides added protection for the RFID tag.
A 4-mm-diameter hole is required to seat the RFID tag. The addition of a 0.8-mm slot provides an improvement in read range, but the RFID tag will also function adequately without it. Further testing is being undertaken to determine if the addition of a 4-mm-diameter hole will degrade the mechanical integrity of the mechanism when subjected to shock, vibration, and variations in temperature.
The tags used with these AR-15 receivers conform to the ISO15693/ISO18000-3 (mode 1) standard for operation in the 13.56-MHz frequency band. The standard specifies passive tags that may only become active if placed in an RF field. As a result, these passive tags do not require a dedicated battery within the firearm.
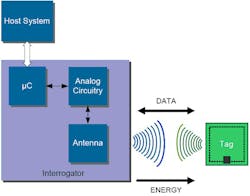
3. This block diagram identifies the components of an RFID system.
The RFID tags are powered from the RF field generated by the external electronic devices (the interrogator/reader) generating the RF field and designed to communicate with (read) the tag. Tags designed to this standard are “vicinity devices” and have a limited read range of approximately 1 m depending on their size and the size and power output from the reader antenna, which is commonly referred to as the interrogator antenna (IA). Figure 3 shows a system block diagram.1 RFID systems using this standard have been used successfully for inventory tracking of high-value clinical products such as implantable cardiac defibrillators (ICDs) and stents (Fig. 4).2
4. One application for RFID tags involves stent tracking in hospital cardiac catheter laboratories.
RF Testing
Numerous readers and IA were studied as part of this project to use RFID tags for firearm tracking. Reader power outputs ranged from 100 mW to 4 W and IAs with 20 to 300 mm diameters were investigated. Read ranges with consistent results varied from 30 to 75 mm depending on the reader/IA configuration. Cellular telephones with near-field-communications (NFC) functionality were found to perform well in reading smaller RFID tags. NFC is a standards-based type of wireless communications that enables the exchange of data between devices over a distance of about 5 cm.
5. This is a midrange reader with a 125-mm IA.
6. This AR-14 firearm is shown positioned over an IA.
Measurements for this study were made using both an industry-standard mid-range reader (Feig model MR101 with 1-W output) with a 125- × 125-mm2 IA (Figs. 5 and 6) and a Samsung Galaxy S3 cellular telephone (Fig. 7). The use of cellphone technology added a great deal of functionality, such as Global Positioning System (GPS) and emergency calling, to practical applications involving firearms.
7. The Samsung Galaxy III is typical of modern smart cellphones, running one of its many applications.
Conventional RFID tags (Fig. 8) were also investigated and were not found to function well when mounted directly over metal. Configurations were fabricated with a shallow cavity below the tag that resulted in reasonable read performance, but the tags were not robust from an environmental point of view.
8. Conventional RFID tags can be supplied in extremely small sizes for unobtrusive attachment to the metal surfaces of firearms.
In time, it’s thought that rugged RFID tags will be available in various formats, and high performance for reasonable cost will dictate their use. The concept of a single 4-mm through hole as the only modification to the LR appeared to be less obtrusive than the other configurations that were investigated. The on-metal tags have also been tested in accordance with the shock and humidity requirements specified by MIL-STD-202 Equipment Qualification testing.
Initial testing required, as a minimum, the capability to reliably read both the tag UID and programmable memory as well as to write and store the programmable memory. Both read and write tests were performed repeatedly with both readers over a quantity of five tags and various distances and orientations. In all testing, it was found that reliable performance can be achieved within a 50-mm range as long as the IA plane was reasonably parallel with that of the tag.
Near-field RFID relies on inductive coupling; the orientation of the magnetic fields must align to achieve optimal read range performance. In order for the tag to become active, the voltage induced by the reader and IA RF field (Vtag) must be sufficient to achieve the minimum level requirements of the RFID chip embedded on the RFID tag. The level of Vtag is a function of the tag size/orientation. The magnitude of the magnetic field strength for an ideal loop may be expressed by:3
Vtag = 2πf0NQB(Scosα) (1)
where N = the number of windings in the tag coil; Q = the tag quality factor; B = the magnetic field strength; S = the area of the tag coil; and α = the tag orientation angle.
The magnetic field strength, B, is generated by a circular IA and may be expressed by:
B = μ0Ina2/2r3 (2)
where I = the IA coil current; N = the number of windings in the IA coil; a = the radius of the IA coil; μ0 = the permeability of free space; and r = the distance from the IA.
RFID has proven to be an effective technology in a laboratory environment, but is still gaining momentum for use in real-world applications. For successful use in many applications, it is essential to read an RFID tag with a sufficient degree of confidence. Some RFID systems currently in use deliver 100% read accuracy.4 Once the RF functionality is achieved for optimal RFID performance, RFID technology can be used for many practical applications.
From the reliability of the read/write performance measured and MIL-STD testing, there’s a high degree of confidence that the proposed application will work in tracking firearm components. It’s worth noting that RFID technology, which has been well adopted by the cellphone industry, has become very affordable over the past few years and offers low-cost integration into almost any application, as will be explained by means of some examples
To verify functionality in a practical environment, a Ruger AR556 was modified (Fig. 9) and fitted with an RFID tag (Fig. 10). To date, over 1000 rounds of NATO 5.56- × 45-mm, 55 grain full-metal-jacket (FMJ) ammunition have been fired through the firearm with the use of a single RFID tag. Most tests consisted of firing 100 rounds per day, with 200 rounds fired in one day, mostly in rapid-fire mode. Rounds were fired at various temperatures (+20 to +95ºF) in an attempt to test the robustness of the RFID tags.
9. Shown is a modified AR-15 LR.
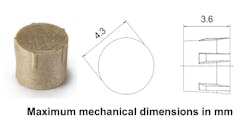
10. These are the dimensions of a typical modern RFID tag.
Over the course of the testing, the RFID read/write performance was recorded, without any failures or degradation in performance. Failure was identified as the inability to read an RFID tag’s UID and read/write programming information, while degradation was identified as a reduction in the read range of the tag.
Proposed Law
In the United States, New Jersey passed the Childproof Handgun Bill into state law on December 23, 2002. This proposed legislation will eventually require that all firearms sold in New Jersey will have some form of mechanism to prevent unauthorized use of a firearm. The law will take effect three years after this type of smart gun is approved by the state. A bill currently in the New Jersey Legislative Assembly, No. 1016, State of New Jersey, is an act concerning personalized handguns that’s meant to revise various parts of the statutory law according to the following specifications:
- A handgun shall be reasonably resistant to being fired by anyone other than its authorized user as defined by New Jersey Statutory 2C:39-1.
- The personalized technology shall be incorporated into the design of the handgun and shall be a permanent, nonremovable part of the handgun and a device or object that is required for the authorized user to fire the handgun.
- The personalized handgun shall not be manufactured to permit personalized characteristics of the firearm to be deactivated.
- The personalized handgun shall meet any other reliability standards generally used in the industry for other commercially available handguns.
This NJ bill also specifically identifies RFID as a possible technology for limiting a handgun's operational use.
One proposed method for ensuring compliance to the proposed legislation is to associate the authorized user of a firearm to the RFID tag embedded within the firearm and an external key fob or cellular telephone. A key fob is a small electronic device typically used in place of a key (as to unlock a door or start a vehicle), or to remotely initiate the action of another device. A cellphone application programmed with the UID of the firearm can be used to trigger the unlock mechanism within the firearm. Since cellphones can read and write to RFID tags, additional equipment external to the firearm would not be required.
As discussed earlier, the receiver is commonly the only federally regulated component of the firearm and will remain with the assembly throughout its life span. Since other components can be replaced, it’s logical for the receiver to store the history of the firearm. Records such as rounds fired, disassembly, cleaning, and inspection criteria are most common data that would be stored in such a location. The bore, firing pin, bolt face, gas ring, and gas key must routinely be inspected and data from reports could be recorded into the tag.
For those law-enforcement officers who are handed an anonymous firearm from storage, it’s prudent to know its most recent history or to update its usage prior to returning the firearm to storage. Performing a 10-second scan of the weapon’s history prior to engagement into an emergency situation could possibly screen out defective or questionable weapons. Cellphone applications with a simple checklist and red-flag indicator are currently being developed that provide a government officer with practical real-time feedback and a reporting mechanism that’s designed to require less than one minute to complete.
The AR-15 is known to “run dirty.” Unlike other gas-activated weapons, the AR-15 valves the gas back into the action where, with every firing of the weapon, hot, carbon-laden gases can be produced that can foul the firearm’s mechanisms. A day of target practice commonly results in a soot-laden, oily contamination that requires some effort to clean.
A firearm used in an anonymous, unknown fashion may require significant routine maintenance that can be effectively tracked and recorded by means of RFID technology. Addition of onboard electronics and sensors can enable the automated updating of the firearm’s use and history into the memory portion of the RFID IC. An example of such functionality is the employment of accelerometers to sense the recoil used to record the number of rounds fired.
Federal law (the Gun Control Act of 1968) regulates that all newly manufactured firearms produced by licensed manufacturers in the United States and imported into the country bear a serial number. For this reason, it’s common to associate the embedded RFID tag’s UID with the serial number of the firearm. This allows recovery of the serial number, assuming that the firearm's serial number has not been obliterated or altered in any way. It would only be practical if the RFID tag were hidden and disguised.
The RFID tag discussed previously (Fig. 10, again) has been sealed into the receiver using black epoxy. Such attachment makes it difficult to locate on the firearm, and would require the use of tools to destroy the RFID tag.
Placing cellphone/RFID technology into the holsters of law-enforcement officers has also been under evaluation for tracking firearm use by those law-enforcement officers. This application triggers a response upon the removal of the weapon from the holster. Low-cost, unobtrusive cellphone circuitry employing NFC and GPS technologies is built into the holster.
When an officer draws his or her weapon, the RFID IC senses this action, which triggers a response to emergency services with the time of the withdrawal of the weapon, the shield number, and the GPS location of the officer withdrawing the weapon. Updating of the location can continue until the officer re-holsters the weapon. This provides emergency services or the officers themselves with the ability to monitor multiple law-enforcement officers and makes it possible to coordinate in-field activities of officers and/or reduce the chance of injuries in a cross-fire situation.
In short, as has been shown though practical measurements, the use of miniature, low-cost RFID tags on metal can be effective for applications involving tracking of firearms, such as AR15, M4, and M16 firearms. Such applications will employ low-cost cellular telephone technology, such as NFC and GPS, that’s unobtrusive and presents significant added value to the firearms in addition to RFID functionality.
The RFID tags evaluated for these applications have shown they meet MIL-STD requirements, providing a high degree of confidence that they can maintain high performance while withstanding environmental stress. This successful implementation of RFID on metal surfaces for tracking firearms is a first step in addressing some of the new laws being proposed for tracking firearms.
Acknowledgment
The author would like to thank Stephen Rogg of Shawsheen Firearms for his help in keeping us safe at the firing range.
Ron Marino is Chief RFID Architect for The RF in RFID.
References
1. Ron Marino, “Item Level RFID Diversity Design,” Microwaves & RF, May 2010.
2. Infineon, Chip Card & Security ICs, SRF 55V02P Short Product Information Ref.:SRF55V02P_ShortProductInfo_2007-06.doc.
3. Youbok Lee, “RFID Coil Design (AN678)”, Microchip, 2002.
4. U. S. Patent 8,313,024, “Storage Cabinet with Improved RFID Antenna System,” November, 2002.