This file type includes high resolution graphics and schematics when applicable.
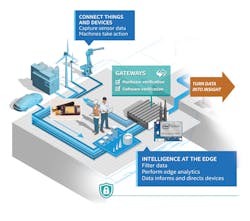
There are so many considerations to take into account when implementing machine-to-machine (M2M) and industrial Internet of Things (IoT) technologies and every aspect must be carefully considered, ranging from cost and power to long-term product-life-cycle challenges and interference.
Even those companies armed with a solid standard—one that is efficient and sufficiently versatile for a variety of applications—may find that innate RF and infrastructure challenges continue to plague this emerging industry. Here are four critical areas to watch out for:
Low Power or Data Rate
The urge to acquire data, control, and intercommunicate throughout a connected-device environment can be quite costly in terms of power. Many wireless-device nodes only need to transmit data in a very limited and infrequent duty cycle. As a result, the power requirements for these types of devices is understandably low. The power requirement will be quite different for devices that are relaying large amounts of data or continuously gathering data from their surroundings.
The tradeoff between power efficiency and data rate extends from the base hardware and wireless protocol used to communicate to the sensors integrated into the platform and the RF environment in which the IoT device is communicating. Generally, a higher data rate and longer range correspond to a higher power requirement. If a device is more sophisticated, in terms of the data it can process and share, it will therefore be more limited in terms of range. It also will be more susceptible to the outside environment.
According to Greg Fyke, marketing director of IoT Wireless Products for Silicon Labs, “Balancing data rate, range, and battery life are challenges for most low-power IoT platforms. An obvious way to increase the wireless transmitter’s range is to boost the transmit output power to the maximum allowable level, but to realize low power in this scenario you have to architect your application to limit transmitter use and maximize the time spent in standby.”
If the competing features of low power, range, and data rate are all critical, more investigation and development are needed for an appropriate wireless standard/protocol.
Standards & Interoperability
With an overwhelming number of proprietary and open M2M and IoT solutions available, there is a great deal of confusion over which to choose and under which circumstance it is best to deploy it. Many organizations are actively working to promote solutions that will unite M2M and IoT technologies—among them, m2mGlobal Alliance, Thread, Internet of Things Solution Alliance, AllSeen Alliance, and the Internet Protocol for Smart Objects Alliance. In addition, many competitors and various industrial partners are teaming to create solutions that can provide the necessary range of operation needed for IoT applications. These efforts involve merging a variety of disparate wireless technologies.
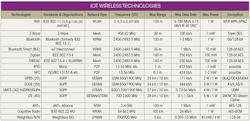
In these organizations, arguments are typically centered on the wireless hardware, software, and standards (see table). A variety of standards, for example, are better suited to certain aspects of applications. Yet some standards are highly versatile. With many of these wireless standards, there are concerns about the cost of adoption and implementation, as well as the risk of obsolescence. As a result, many of the alliances are focusing on creating solutions that optimize the benefits of various existing wireless standards. In doing so, they hope to create standards and technologies that can coordinate devices operating on different standards.
“Recently, in M2M, we are seeing the development of platform applications that enable users to almost do a point-and-click app solution, such as Apple iOS, Thingworx, and our business,” notes Alex Brisbourne, CEO of Kore, Alpharetta, Ga. “These companies are creating downstream libraries of pre-designed applications and solutions based on a variety of technologies. So if customers want a sensor application, they can choose from a variety of sensor providers and quite quickly build those solutions. These uniting platforms are still quite early in gestation. But this approach removes the mystery from having to deal with the numbers of proprietary devices and learning each individual one.”
Security & Device Sophistication
When choosing or developing an M2M/IoT solution, another compromise arises in how secure the device or system needs to be. The level of security usually depends upon the application, which requires anything from maintaining consumer privacy to limiting cyber attacks against utilities. Unfortunately, as we rely more heavily on these systems, more opportunities arise for malicious conduct against them.
As noted by Daniel G. Steele, director of the OEM, Utility, and Energy Market for Freewave Technologies, “M2M, from a security perspective, has probably changed dramatically after 9/11. Some people are more aware from the cyber-attack side of the fence and informed about a lot of the attacks seen by SCADA networks. These issues are on everybody’s mind now—especially with smart-grid applications and how they keep their networks secure.”
From corporate espionage to denial-of-service (DOS) attacks, many connected systems face regular threats. As a result, Steele says, “Security needs to increase along with all the performance benefits we like to see. The focus shouldn’t just be on what we expect with speed and connectivity but also, how secure is everything? We have to make sure no one is eavesdropping on our data packets or conversations.”
Generally, adding security features to wireless systems requires more overhead in each packet sent. It also means adding components within the electronics. “There is a cost-analysis side of security features,” says Kore’s Brisbourne. “For example, if you are putting tens of thousands of devices in a network, how much processing can you have on that device for security? The security sophistication at the device level affects the relative balance of device cost, performance, and power. It is safe to say that there is a specific tension in a design engineer, urging him to look into this.”
This file type includes high resolution graphics and schematics when applicable.
Interference/Failures & Spectrum
This file type includes high resolution graphics and schematics when applicable.
To prevent interference and failure modes in M2M/IoT devices, reconfigurable networks must be created to ensure adequate operation. A variety of new networking standards and updates to old standards include techniques for networks to automatically decide workarounds. These adaptations are designed to work in scenarios ranging from fatal node failure to interference issues.
“Devices can fail so it is important for networks to have built-in resiliency,” says Silicon Labs’ Fyke. Mesh networks, such as ZigBee and Thread, are designed to self-heal and the network has the ability to intelligently redirect traffic if a device node is no longer available. In the event of a node failure, routes are dynamically updated to realize the most optimal path through the new network configuration. These fail-safe mechanisms in mesh networks ensure that messages can reliably reach their destination. The market won’t tolerate an IoT platform where the lights turn-on ‘most’ of the time. When you flip a light switch, the light must turn on every time.”
As more wireless devices operate in a frequency swath within the RF environment, the greater the noise and interference will be in those frequencies. Many unintended and non-congestion-related aspects of interference, such as intermodulation and nonlinear effects, lead to other noise-causing issues. These performance-degrading issues exist, regardless if the frequency band is licensed or unlicensed.
Freewave’s Steele says, “Another great challenge and the biggest complaint of the operators in the industry is why hasn’t the FCC opened up more dedicated spectrum specifically for SCADA and M2M systems. The ISM band is great, along with the uniband and 5-GHz bands. But it is a double-edged sword if you don’t have a radio product that can adapt and work around the noise potential.”
He adds, “If you don’t engineer the system well for noise, it can be your worst enemy. There are licensed systems around. With licensed systems, though, you generally have narrow bandwidths and can’t operate at high capacity.”
Do Endless Possibilities Equal Endless Confusion?
As mentioned, several organizations have been looking to create standards and technologies that will serve as the wireless “glue” that joins the various standards and wireless technologies. From a component level all the way to a protocol level, devices will then need to be optimized for flexible operation over common wireless standards. The resulting solutions could range from software-defined operation to highly capable, though specialized devices that are geared toward power optimization using a few critical wireless technologies.
“Traditionally, to enable multi-protocol support, one would need to use multiple radios, which can be expensive,” says Fyke. “If you had a radio that was designed to support multiple protocols by time-slicing operation, you could enable multi-protocol support at a much lower cost point and still be able to address some really exciting use cases.”
Although there are still many standards and challenges associated with implementing M2M/IoT networked systems, significant progress is being made in uniting current technologies. These approaches may take the form of new wireless standards or even devices that can operate using a variety of wireless standards and frequencies, which will, of course, be based on sophisticated protocols. Whatever solutions end up dominating, they will have to overcome the challenges of security, node failure, and ever-growing interference.
This file type includes high resolution graphics and schematics when applicable.